How to Select the Right Cisco Switches for Your Local Area Network?
Creating network designs for people is not an easy task, for many factors and requirements need considering. It’s the fact that most organizations do not upgrade their LAN to prepare for the future – most of them don’t touch the network as long as it is running properly and supporting the user’s applications. When starting the planning process for putting a secure voice system on the network, which takes the network requirements to another level.

There is a lot more to consider than QoS for putting voice on the LAN, although that is what the discussion is usually centered around. The LAN also has to have a number of other attributes:
- Secure - with voice on the LAN, the switches must have security features that can prevent them from getting attacked with MAC address floods, rogue DHCP servers, gratuitous ARP’s changing the default gateway, and other attacks that can be launched by malware.
- Fast - If voice goes through multiple switches, each hop can add latency. Instead of store and forward of the ethernet frames, switches should use cut-through to move things along. Server and uplink speeds should be gigabit, while for most organizations 10/100 Mbsp to the desktop is just fine.
- QoS - As discussed above. This comes into play mostly in uplinks. When remote access layer closets are connected back to the distribution layer, there is a choke point in the LAN. Any choke points require queuing to prioritize the voice.
- Reliable - Long Mean Time Between Failure, well tested code to limit bugs, good support from the manufacturer in case there is a software or hardware issue.
- Managable - The switches have to be able to be managed remotely, have SNMP information, be able to log, and be configurable. GUI interfaces are ok, but there is nothing like a solid command line interface for rapid configuration, troubleshooting, and repair.
- Power Density- Switches have to be able to support the power density of the planned devices. Most switches cannot power all ports at the highest levels.
- Power and Cooling – Since IP phones are powered from the switches, all access layer switches will require properly sized UPS’s. A basic switch consumes about 60 Watts. A 48 port switch with 15 Watt phones plugged into every port will require at least 600 Watts. Put a few of those switches in the closet an you are looking at not only a much bigger UPS, but also better cooling.
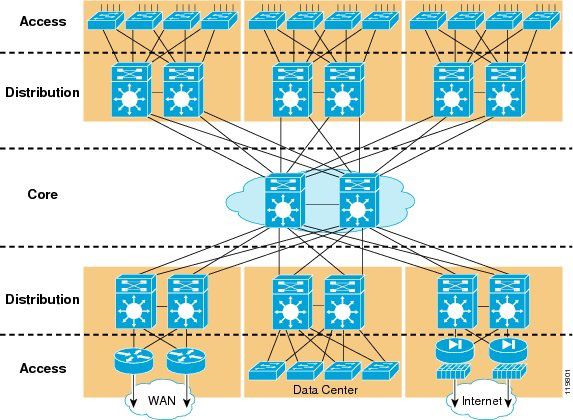
- Redundant Design – The only place that there should be a single point of failure is at the access layer in the closets. If a switch fails, only the devices connected to that switch should lose connectivity – all others should work around the issue. In most cases that means dual uplinks from each closet to a redundant distribution layer at the core.
An excellent reference to everything discussed above is the Cisco Campus Network for High Availability Design Guide. This drawing shows both redundant uplinks and the single points of failure that are acceptable:
When all the requirements for a good LAN that can support voice are evaluated, it turns out that it prepares the network for future requirements as well, like IP security cameras, wireless access points, and other devices that may hang off the LAN.
It is certainly possible to build out a LAN with non-Cisco switches, but there are so many little things that are useful with Cisco switches, and they tend to be price competitive, that it is usually best to go with them. For example, one of the most useful tools is Cisco Discovery Protocol, which lets you see what other CDP devices are connected to an individual switch. I use this all the time to work my way through a network and find out where devices are located.
Having set a baseline for what we are looking for in a LAN switch, we can overview a variety of Cisco switches that are available and largely required by small to large businesses. And most of them serve a useful purpose for different situations.
Cisco Catalyst 2960 Series – a type of useful, versatile switch. It is layer 2 only, so no routing. The 24 port 10/100 POE version is great. It includes two gigabit dual-personality uplink ports, so a stack can be linked together, and then the top and bottom of the stack can be connected by fiber to the distribution switches. This switch is good and popular.
Cisco 3560 Series– Similar to the 2960, but has a few more features. This is a layer 3 switch, and has three different classes of IOS. The IP base includes static routing, EIGRP stub, but no multicast routing. IP services includes the full routing features set. IP Advanced Services includes IPV6 on top of everything else. The SFP ports have to be populated with either copper or fiber gig SFP’s to uplink.
Cisco 3750 – This is just like the 3560, but with one big difference. The 3750 includes two Stackwise connectors on the back of the switch, allowing up to nine switches to be stacked together using a 32 Gbps backplane speed. The stack is managed as a single switch, and uplink ports on different switches can be connected together with EtherChannel so that multi-gigabit closet uplinks can be obtained. For an inexpensive distribution layer, a small stack of 3750 switches is ideal. The entire stack is limited to 32 Gbps of throughput, so this is not a good server switch for more than about 20 servers.
Cisco 4500 – This is a chassis switch that is designed to be used in the access layer. The internal design is optimized for connecting a bunch of users and uplinking out of the closet, since the internal connections the different thirds of each blade is limited to 2 Gbps in most of the linecards. The latest version of the blades and supervisor are faster, but are still oversubscribed, so this should not be used for a distribution or server switch. It is a great access layer closet switch for high density (>200 users) gigabit POE to the desktop.
Cisco 3560E Series– The E version of the 3560 switches are gigabit to the desktop and 10 gigabit uplink and aggregation. They also have modular power supplies so that every port on a 48 port switch can be powered to the highes level if required.
Cisco 3750E – gigabit speed, 10 Gbps uplinks, and Stackwise+ for switch interconnection. Stackwise+ is twice the speed of Stackwise at 64 Gbps, but has a much higher comparative speed since all traffic that is on one switch can stay on the switch, whereas with Stackwise on the 3750′s all traffic traverses the Stackwise link.
Cisco Catalyst 6500 Swithces– Excellent switch, very useful as a distribution and server switch. The switch has three backplanes, and it is worthwhile looking at the connection speed of the supervisor engines and blades before making a decision. The legacy backplane is still available using the Sup720; it is a 32 Gbps shared backplane. New blades use either CEF256, which is a 8 Gbps connection, or CEF720, which uses dual 20Gbps connections.
- The Cisco 6500 blades can have distributed routing features, or dCEF. These are typically not required except for the most challenging networks.
- The most cost-effective and reliable method for setting up a 6500 is to use a single chassis6509 with redundant power supplies, redundant supervisor engines, dual 6748 gigabit blades for server connectivity, and dual 6748 fiber uplink blades for connecting remote wiring closets.
- The Cisco 6509 has no limitations – any blade can go into any slot. The Catalyst 6513 has more slots, but only the bottom four can accept the CEF720 blades, the top seven slots connect at CEF256 or slower.
- My preference is to usually use this box as just a switch, and put routing, firewall, wireless control and other functions in dedicated boxes, but there are certain situations where the ability to put services modules like the ACE module, IPS modules, or Firewall services module in the 6500 solve a specific technical problem.
So, some examples of good designs:
- If there are between 500 and 2000 hosts on a LAN, then single or dual 6500′s at the core/distribution layer are appropriate. Stacks of 3750′s or 2960′s in the closet with gigabit uplinks back to the distribution layer are appropriate.
- For between 100 and 500 hosts on a LAN, then a stack of 3750E or 3750 switches at the core/distribution layer and a stack of 2960′s in the closets would be a good design for most organizations.
- For <100 hosts, a good design is dual 3750′s at the distribution layer with 2960′s for access layer. If price is the deciding factor then a stack of 2960′s is appropriate.
Examples of non-optimal designs that I have seen:
- Putting a single Cisco 3750 in an access layer closet. There is no reason for this, as the primary benefit of the 3750 is its Stackwise system. If there is only one, then no stacking is required.
- Adding dCEF capability to a 6500 when there is very little routing to be done in the system, and the 6500 is nowhere near hitting its performance limit with all routing being done in the supervisor engine.
- Having a mismatch between power draw and power supply on the switch. This can happen from having power supplies that are too small, or loading too many POE devices onto an underpowered 48 port switch.
One of the most useful devices to increase reliability of the switching infrastructure is a backup power supply. One of my rules of thumb is that moving parts break first, so the most likely item to fail in the switch is the power supply and/or cooling fans. Every Cisco switch and most of the smaller routers have a DC port in the back. That is for backup power.
The Cisco RPS675 can be used as backup power. It has dual power supplies, and can connect to six different devices. If those devices ever lose their power supply, then the RPS box will provide power via the DC power port, and everything will contine to run. The only tricky thing is ordering the correct cables. There is one set of cables for E versions of switches, and another set for all other devices.
Putting together a LAN upgrade design is a relatively straightforward process. The difference between a good design and a poor one really come down to the details. No one wants to get a cheap network that will not handle the needs of the organization in the next few years and have to be replaced, and converseley most organizations would not want to pay for an oversized network that is too expensive.
It is best to get a design done from a reseller that regularly sells deploys the products they are recommending. Good VAR’s will stay on top of the new products that are out, and will change their recommendations are based on the customer’s needs and budget. I would argue that a good VAR can put together a better design than a sales engineer from a manufacturer. The VAR is responsible for making it work within budget, whereas the manufacturer will not do the installation, and is compensated for selling as much equipment as possible.
More Cisco hardware guide and info you can visit: http://www.router-switch.com/Price-cisco-switches-cisco-switch-catalyst-3560_c22?page=3



/image%2F1490247%2F20190117%2Fob_9629a3_new-cisco-9000-family-members.png)
/image%2F1490247%2F20181221%2Fob_c62717_explore-the-nexus-400g-portfolio.png)
/image%2F1490247%2F20181127%2Fob_43ede7_cisco-catalyst-9800-series-wlc.jpg)
/image%2F1490247%2F20181026%2Fob_214c75_cisco-ie-series-switches.png)
